Generating Rules
CloudSigma generates Sigma detection rules from three input types: URLs (threat blogs and advisories), CVE IDs, and raw text. Each input goes through the same pipeline: ingest → extract TTPs → generate rules → validate → convert.
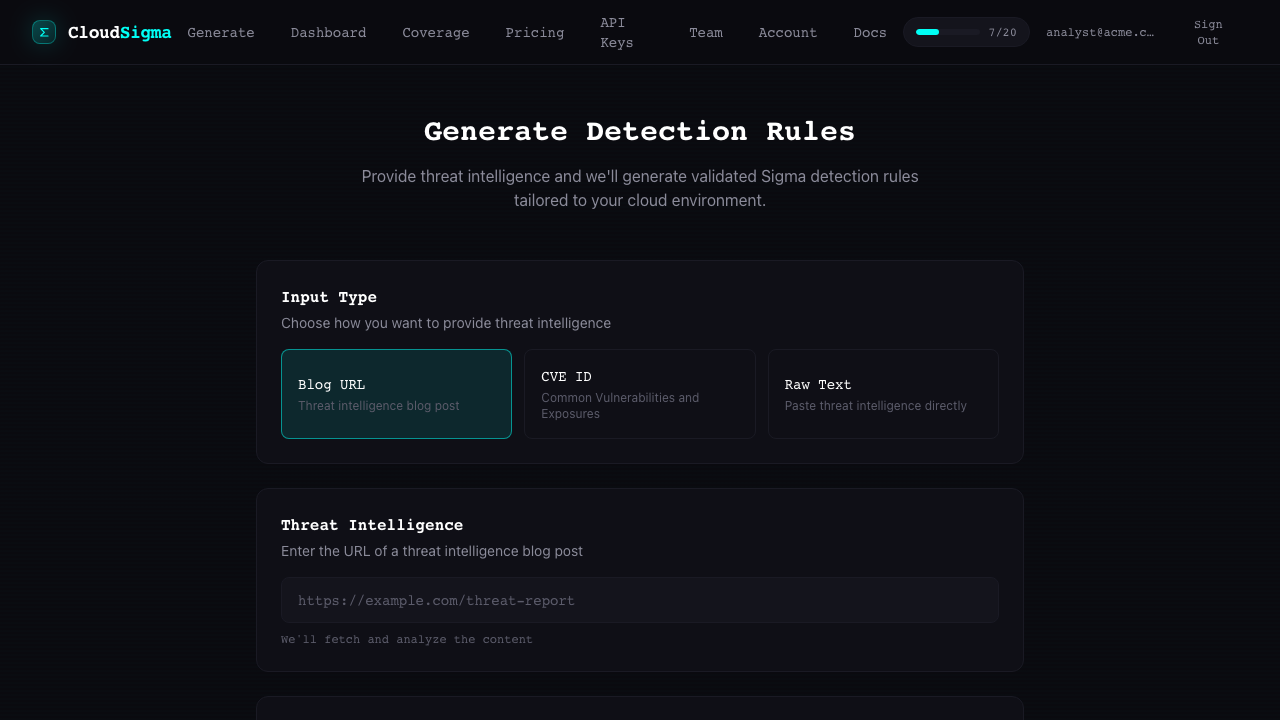
Input Types
URL Input
Submit a URL to a threat advisory, blog post, or security bulletin. CloudSigma fetches the page content, extracts threat intelligence, and generates rules.
curl -X POST https://cloudsigma.a13e.com/v1/generate \
-H "Authorization: Bearer YOUR_API_KEY" \
-H "Content-Type: application/json" \
-d '{
"inputType": "url",
"url": "https://www.cisa.gov/news-events/cybersecurity-advisories/aa24-242a"
}'Best for: Published threat advisories, vendor security blogs, CISA alerts, unit reports.
URLs must be publicly accessible. CloudSigma fetches content server-side with a 5 MB size limit. Private or paywalled pages will fail.
CVE Input
Submit a CVE ID to generate detection rules for a specific vulnerability. CloudSigma enriches the CVE with data from NVD, MITRE, and linked references.
curl -X POST https://cloudsigma.a13e.com/v1/generate \
-H "Authorization: Bearer YOUR_API_KEY" \
-H "Content-Type: application/json" \
-d '{
"inputType": "cve",
"cveId": "CVE-2025-1974"
}'Best for: Specific vulnerabilities you need detection coverage for.
The enrichment process fetches up to 2 reference URLs (max 500 KB each) from trusted domains including NVD, MITRE, CISA, GitHub Security Advisories, and major vendor blogs.
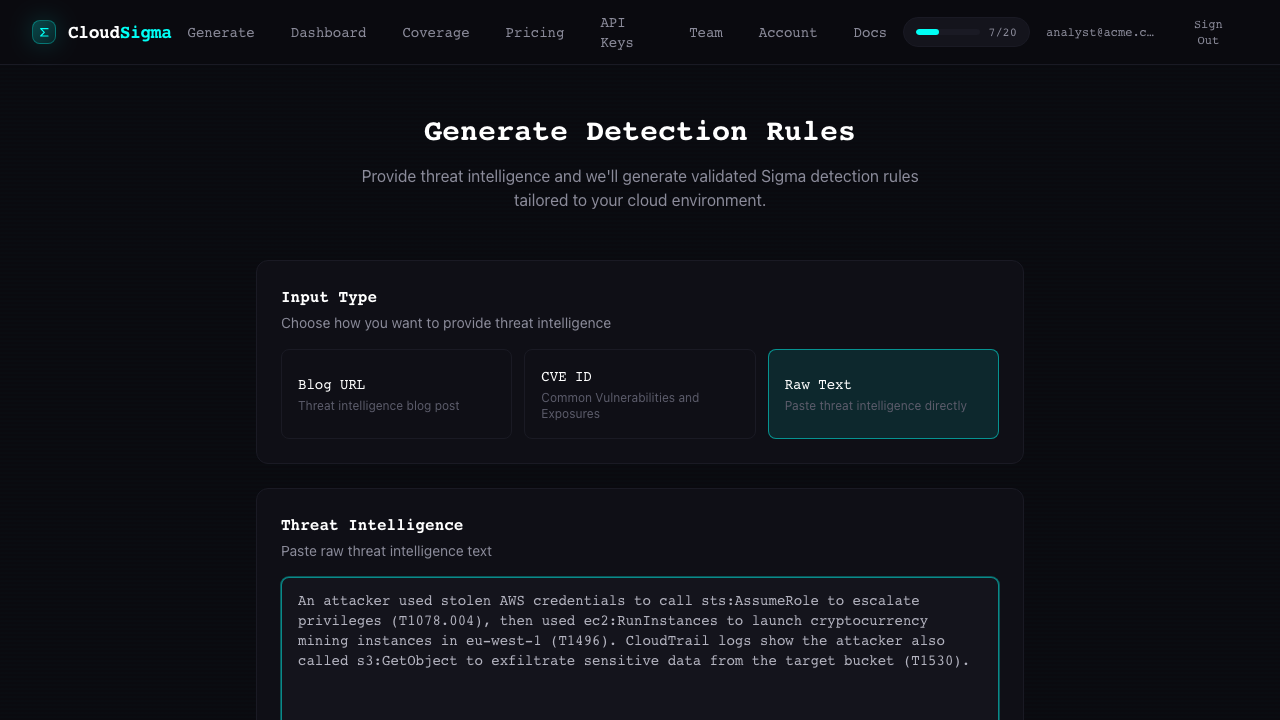
Text Input
Paste raw threat intelligence text directly. Useful for internal reports, email-based indicators, or content from sources that require authentication.
curl -X POST https://cloudsigma.a13e.com/v1/generate \
-H "Authorization: Bearer YOUR_API_KEY" \
-H "Content-Type: application/json" \
-d '{
"inputType": "text",
"text": "The threat actor leveraged compromised AWS IAM credentials to create new access keys (T1098.001) and establish persistence via Lambda function modifications..."
}'Best for: Internal reports, proprietary intelligence, content behind paywalls.
Maximum text length: 50,000 characters.
Options
You can customize rule generation with the options object.
Target Providers
Limit rule generation to specific platforms. By default, rules are generated for all 13 platforms where the detected TTPs apply.
{
"inputType": "url",
"url": "https://example.com/advisory",
"options": {
"targetProviders": ["aws", "gcp", "azure"]
}
}See Supported Platforms for all valid provider IDs.
Target SIEMs
Limit SIEM conversions to specific backends. By default, rules are converted for all 6 backends.
{
"options": {
"targetSiems": ["splunk", "sentinel"]
}
}Valid values: splunk, sentinel, elasticsearch, chronicle, opensearch, google_secops.
IOC Rules
Control whether IOC-based rules (IP addresses, domains, hashes) are generated alongside behavioral rules.
{
"options": {
"includeIocRules": false
}
}Default: true. Set to false if you only want behavioral TTP-based rules.
Pipeline Steps
When you submit a request, the pipeline executes these steps:
- Ingest — Fetch and parse the input (URL content, CVE data, or raw text)
- Classify — Determine if the content contains actionable threat intelligence
- Extract TTPs — Identify MITRE ATT&CK techniques with confidence scoring
- Filter — Remove host-level, unknown, or low-confidence TTPs
- Generate Behavioral Rules — Create Sigma rules grounded against the gold corpus
- Generate IOC Rules — Create indicator-based rules (if enabled)
- Deduplicate — Remove functionally identical rules
- Validate — Check rules against pySigma for syntax and field correctness
- Convert — Transform Sigma YAML to SIEM-native query languages
- Watermark — Add metadata watermark for free-tier users
Tips for Best Results
- Be specific with URLs — Direct links to advisories work better than index pages
- Include context in text input — Mention specific techniques, tools, or platforms
- Start with cloud platforms — AWS, GCP, and Azure have the richest gold corpus coverage
- Use target providers — Narrowing platforms reduces noise and speeds up generation
- Check pipeline notices — The
pipelineNoticesarray in the response contains warnings about skipped TTPs or detection gaps